Information Security Tips (May 2024) – Security Considerations When Using Public AI
Artificial intelligence (AI) platforms provide users with a variety of powerful tools and services that can help them to accomplish a variety of tasks, from data analysis to machine learning. However, there are some security risks to be aware of when using public AI platforms.
Below are some security tips to protect your data and privacy:
- Choose a reputable platform: Choose a platform with good reputation and research its security and compliance record.
- Understand the platform’s privacy policy: Read the platform’s privacy policy before using it. Understand how the platform collects, uses and shares your data.
- Be careful of what you share: Only share the data you need to complete your tasks. Avoid sharing any sensitive, confidential data, unpublished work information or research results.
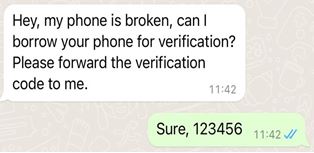
- Use strong passwords and enable two-factor authentication: Create strong passwords for your accounts and enable two-factor authentication.
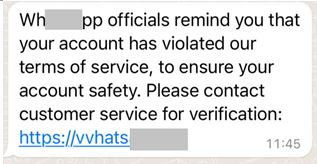
- Beware of phishing and scams: Do not click on suspicious links or enter your account information on unverified websites.
- Keep your software up to date: Keep your operating system and AI platform software up to date.
- Report suspicious activity: If you notice any suspicious activity, report it to the AI platform’s support team immediately.
By following these security tips, you can help protect your data and privacy while using public AI platforms. If you need further information on “AI privacy” and “Data Anonymization Processing”, you can refer to the relevant information published by the Personal Data Protection Bureau (PDPB): https://www.dspdp.gov.mo/en/references_detail/article/kzw3p0kz.html